What is identity theft?
Identity theft, as it states, is when someone steals another person’s identity, i.e. personal information such as a social security number, with the intent to commit fraud, usually for economic gain. Obviously aware that they have stolen another person’s identity, the offender’s intention is to use it to create new accounts or tamper with existing accounts under the stolen identity.
All sensitive personal information is at risk, as the person committing the crime will have access to a list of resources connected to the stolen identity. These resources can then be used to create accounts in industries such as medical, financial, insurance, gaming and so on.
Whatever an individual might have, that is beneficial to the identity thieves, is up for grabs once an identity has been stolen.
Identity theft is a major problem worldwide, but specifically in Europe with one in five Europeans having experienced identity fraud in the last couple of years. Furthermore, living in a more digitized world, identities can be easily stolen with a new victim of identity theft occurring every two seconds.
What is the difference between identity theft and identity fraud?
As mentioned above, identity theft is the act of stealing another’s identity with the intention of using said identity to open new accounts or manipulate existing accounts. Fraud, on the other hand, is the act of stealing information and misusing the personal information and existing accounts of the victim.
For example, say you are a victim of a data breach and someone uses your credit card to make unauthorized purchases. This is an act of fraud. But, if the thief took the information and created a new credit card account or used the identity to apply for a job, this would be considered identity theft.
Though very similar, identity theft cannot happen without fraud since identity fraud is the use of the stolen information, but fraud can happen without leading to identity theft. Either way, this crime affects both the individuals whose identities were stolen and the businesses where the stolen identity has been used to make fraudulent transactions.
What are the different types of identity theft?
There are many different types of identity theft, each with its own unique set of challenges. The most common types include the following:
Financial
The most familiar type, this is when a thief gains access to your financial accounts and credit cards and uses them to make unauthorized charges.
Social Security
This occurs when someone has gained access to another person's social security number and uses it to apply for credit cards, loans, or other types of benefits.
Medical
Medical identity theft occurs when someone uses another person's insurance information to receive medical care or services.
Tax
Tax identity theft occurs when someone uses another person's social security number to file a false tax return and claim a refund. Identity thieves may also apply for government benefits such as unemployment or food stamps.
Synthetic
Synthetic identity theft is a type of ID theft where a criminal combines real ID information with fake information in order to create a new identity. This new identity is then used to open new fraudulent accounts and make fraudulent purchases.
Child
Child identity theft is when personal and sensitive information of a child is stolen from a criminal in order to obtain money, employment, or possibly avoid arrest. Children are easier targets since they do not have as much information associated with their names and are unaware if their identity has been stolen.
Criminal
Criminal ID theft is when a person poses as someone else in order to avoid arrest, a warrant, or background check.
What industries are affected by identity theft?
This list can be quite long when it comes to ID theft because once an identity is stolen, thieves have access to almost anything, as previously mentioned. Below are just some of the industries that are affected by identity theft.
Financial Institutions
For starters, and perhaps the most obvious, is the financial industry. Financial institutions are hit the hardest, with identity theft costing them billions of dollars each year. Due to the industry's large accounts and vast amounts of personal information available, criminals see it as their pot of gold. Credit cards and bank accounts can be easily opened with data from a stolen identity or multiple identities.
Insurance
Additionally, insurance is also very vulnerable and high on the list since it too also deals with financial transactions. Plus, insurance companies have access to a plethora of data from their clients and provide the perfect target for hackers.
Gaming/esports
Identity theft in gaming and esports is also becoming more popular as well. According to a study, more than a tenth of gamers have had their identity stolen costing billions of dollars worldwide. Hackers can steal not only items within the gaming world, but also credentials of the players, leading to fake accounts.
Travel/Mobility
Another industry, which can see a lot of ID theft, is the travel and mobility sectors. Under the umbrella term “hospitality,” this industry is ever revolving due to people coming and going. Identities can be stolen, and tickets or reservations can be bought under the stolen identity or new accounts can be opened. Being such a fluctuating business, this can be ideal for hackers and identity thieves.
Crypto
One other industry, worth taking a look at, is crypto. Continually on the rise, crypto has become more mainstream, thus peaking the interests of fraudsters. Vast amounts of money are being transferred worldwide and identity thieves and fraudsters find weaknesses within the system in order to create new accounts or use stolen identities to take over existing accounts and empty wallets of any available coins. Regulations are therefore a needed safety measure from such fraudulent actions.
How does identity theft occur?
Identity theft can occur in many ways, including old-fashioned ways such as someone stealing your wallet, someone making a copy of your credit card, or an individual stealing your mail.
However, today digital identity fraud is more common, especially with most people doing everything digitally due to the pandemic and use social media quite often. Identity theft can occur online through phishing scams, downloading malware that steals information, using insecure wireless networks, sharing passwords, or having information stolen from a data breach of a company.
What are some examples of identity theft?
ID theft can take many forms as mentioned above. A few examples of ID theft might look like:
-Stealing someone's social security number in order to open new accounts or lines of credit in their name
-Making fraudulent charges on an existing account
-Posing as someone else in order to obtain sensitive information, such as medical records or financial statements
-Filing a false tax return in someone else's name in order to receive a refund
ID theft can cause not only a lot of financial damage such as ruining credit reports, but also emotional stress, so it's important to be aware of the different ways it can occur. By understanding how ID theft happens, a person can better protect themselves and their family from becoming victims.
How can a business prevent identity theft?
With regulations in place requiring businesses to ask for more KYC data from their clients, businesses are left with the challenge of safely storing this info, so breaches don't occur. Thus, having large amounts of personal data on file from their clients, digital identification procedures are boosting ID theft. Therefore, businesses have a large responsibility when it comes to clients’ data.
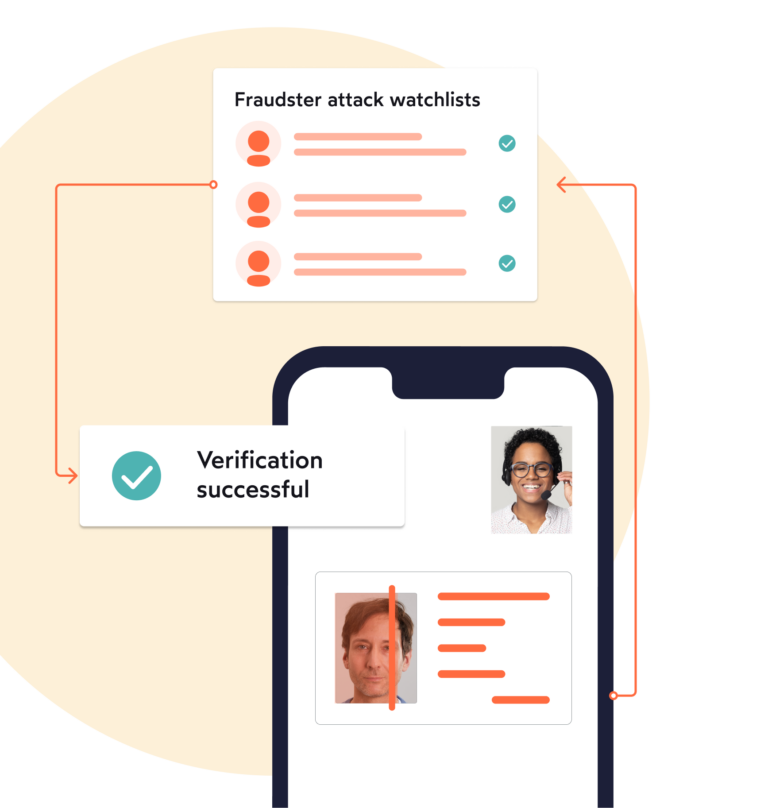
In order to prevent identity theft from occurring in a client base, strong KYC processes as well as AML Monitoring and Screening should be put in place. This can be achieved through products such as AutoIdent, VideoIdent and eID, with all meeting regulatory KYC needs and being AML compliant.
How can your customers prevent identity theft?
Despite the many ways an individual's identity can be stolen, there are also ways to prevent this from happening. Clients should keep the following in mind:
- Have up-to-date security software.
- Pay attention for potential spam and scams. Don’t automatically click on links from emails that may seem safe. Check with the sender or look-up the site before proceeding.
- Use strong passwords.
- Don’t share passwords.
- Only use reputable websites.
- Use a secure network.
- Stay alert. Pay attention to anything that may seem insecure.
- Have secure social media accounts.
Reporting identity theft – What happens when your identity is stolen?
When a person's identity has been stolen, thieves will likely be using the information they gathered in order to commit acts of fraud such as using the information to their advantage and racking up debt under the individual's name.
This will have a major impact on the victim's life. Therefore, once a person has discovered that their identity has been stolen it is important to report this to the proper authorities. Taking immediate action is necessary in order to recover from identity theft.
The first step in a recovery plan is to contact the credit reporting agencies and ask them to place a fraud alert on your file. This will make it more difficult for someone to open new accounts in your name. You should also contact your bank or credit card companies to let them know about the situation and close any accounts that have been compromised. Finally, you should file a police report so that there is a formal record of the crime. By taking swift action, you can help to minimize the damage caused by ID theft and help protect yourself for the future.
What is the punishment for identity theft?
Identity theft is a serious offense that can have long-lasting consequences. If a person is convicted of identity theft, they may face fines, jail time, and a criminal record, as well as be required to compensate the victim for financial losses. However, the punishment will vary depending on the severity of the crime and the jurisdiction in which the person is convicted.
In some cases, identity theft is a felony offense, which means the offender could spend years in prison. In other cases, identity theft is a misdemeanor offense, which carries a maximum sentence of up to one year in jail. Regardless of the classification, identity theft is a serious crime that can have significant repercussions.
In the end, if someone is convicted of ID theft, they will likely find it difficult to get jobs, rent apartments, and obtain loans in the future.
Rising identity theft increases need for Identity Verification
Ever since the outbreak of the COVID pandemic, there has been a global increase in identity theft risk. Today, one in 15 people using the internet is a victim of identity theft according to Legal Jobs. Thus, safeguarding a digital identity is important.
As ID theft affects millions of individuals around the world, costing trillions of dollars in loss, companies have become aware of the extreme necessity and usefulness of digital identity verification. Therefore, a KYC Check is key for businesses so they know who they are working with and that they're trustworthy.
Whether simply proving a person’s identity through having them take a picture of their ID, proving their identity through video or even NFC-based technology, digital identity verification is particularly important and can help reduce the rising cases of identity theft. And IDnow’s products are here to assist in this endeavor.
Overall, no matter the industry, personal data is there for the taking and no industry is immune to identity theft. Nevertheless, some industries are more valuable and thus more susceptible compared to others, so it’s important to take precautions in order to prevent an identity theft attack.
ID Fraud Report 2022—Identities in a digital-first world